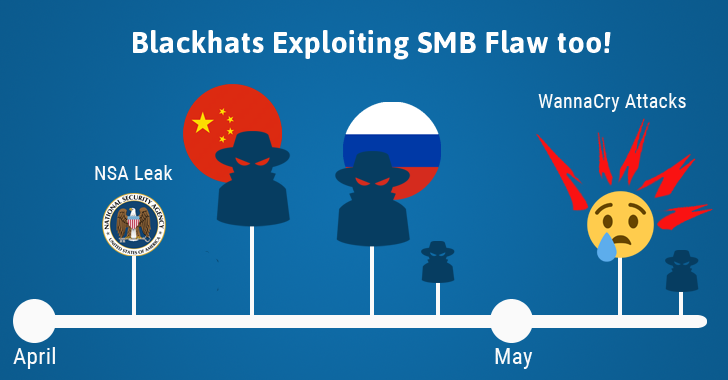
Since the Shadow Brokers released the zero-day software vulnerabilities and hacking tools – allegedly belonged to the NSA’s elite hacking team Equation Group – several hacking groups and individual hackers have started using them in their own way. The April’s data dump was believed to be the most damaging […] .
Category: Social Media & Crime
Zomato Hacked; Hacker Puts Up 17 Million Users’ Emails and Passwords On Sale
If you ever ordered food from Zomato, You should be Worried! India’s largest online restaurant guide Zomato confirmed today that the company has suffered a data breach and that accounts details of millions of its users have been stolen from its database. In a blog post published today, the […] .
Bell Canada Hacked: Data of 1.9 Million Customers Stolen
While we all were busy in the WannaCry ransomware menace, two separate data breaches have been reported, one in DocuSign , a major provider of electronic signature technology, and another in BELL, Canada’s largest telecommunications company. Canadian mobile phone, TV, and internet service provider Bell on Monday confirmed that […] .
WannaCryptor wasn’t the first to use EternalBlue: Miners misused it days after Shadow Brokers leak
The massive campaign that spread the WannaCryptor (aka WannaCry) ransomware wasn’t the only large-scale infection misusing the EternalBlue and DoublePulsar exploits, leaked by Shadow Brokers. The same mechanism has been misused by black hats as early as the end of April, when they opted for off-the-shelf Monero cryptocurrency mining […] .
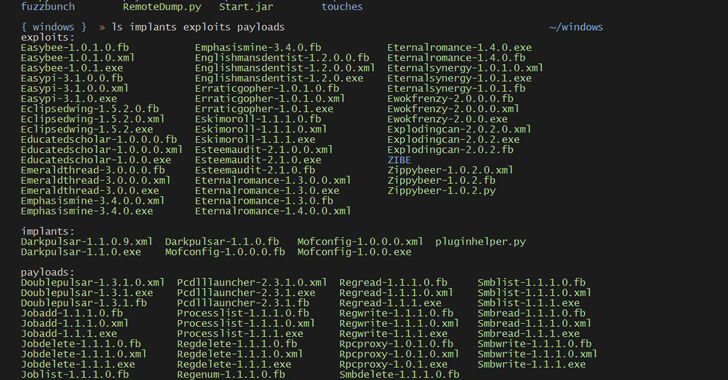
Latest Hacking Tools Leak Indicates NSA Was Targeting SWIFT Banking Network
Latest Hacking Tool Leak Indicates NSA Was Targeting SWIFT Banking Network The Shadow Brokers – a hackers group that claimed to have stolen a bunch of hacking tools from the NSA – released today more alleged hacking tools and exploits that target earlier versions of Windows operating system, along […] .
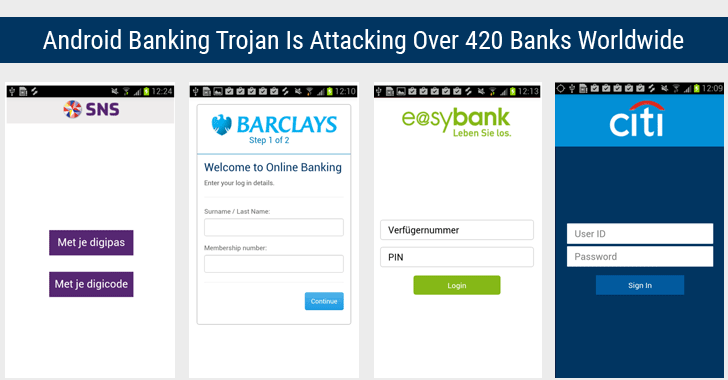
Android Trojan Targeting Over 420 Banking Apps Worldwide Found On Google Play Store
android banking malware Do you like watching funny videos online? I am not kind of a funny person, but I love watching funny videos clips online, and this is one of the best things that people can do in their spare time. But, beware if you have installed a […] .
Hackers Can Steal Your Passwords Just by Monitoring SmartPhone Sensors
Do you know how many kinds of sensors your smartphone has inbuilt? And what data they gather about your physical and digital activities? An average smartphone these days is packed with a wide array of sensors such as GPS, Camera, microphone, accelerometer, magnetometer, proximity, gyroscope, pedometer, and NFC, to […] .
Germany Bans Facebook From Collecting WhatsApp Data
German Bans Facebook From Collecting WhatsApp Data Just last month, the most popular messaging app WhatsApp updated its privacy policy and T&Cs to start sharing its user data with its parent company, and now both the companies are in trouble, at least in Germany and India. Both Facebook, as […] .
Apple Tracks Who You’re Chatting Using iMessage — and Shares that Data with Police
Doing conversations with your friend on iMessage and thinking that they are safe and out of reach from anyone else other than you and your friend? No, it’s not. End-to-end encryption doesn’t mean that your iMessages are secure enough to hide your trace because Apple not only stores a […] .
In-Brief: Spotify Hack, Secret of Chrome OS, MIT Bug Bounty, Nanowire Batteries
1. Spotify Hacked! Change your Password ASAP If you are one of the millions of people around the world who love to listen to music on Spotify, you may need to change your password immediately. Has Spotify been hacked? The company says no, but some Spotify users have claimed […] .
Car Hacking ? Scary, But Now it’s REALITY!
Next time you find yourself hooked up behind the wheel, make sure that your car is actually in your control. Hackers are now able to break into hundreds of thousands of vehicles on the road. Car hacking is a hot topic today and until now it was performed only […] .
Protecting Our Individual Freedoms in a Digital World
PSFK talks to Nuala O’Connor about the importance of advocating for basic human rights in the online space PSFK talks to Nuala O’Connor about the importance of advocating for basic human rights in the online space Innovation is the new currency in today’s Idea Economy. In recognition of the […] .
Panicked over massive data breach? You should be
Government data breach affected more than 20 million 01:14 Douglas Rushkoff writes a regular column for CNN.com. He is a media theorist, the author of the book “Present Shock: When Everything Happens Now” and professor of media studies at the City University of New York’s Queens College. This commentary […] .
Educating Citizens on Protecting Their Online Identities
PSFK speaks to Nico Sell, co-founder of the world’s most secure peer-to-peer encrypted messaging system, about the perils of digital security PSFK speaks to Nico Sell, co-founder of the world’s most secure peer-to-peer encrypted messaging system, about the perils of digital security Innovation is the new currency in today’s […] .
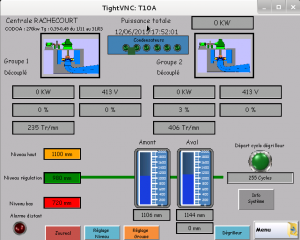
SCADA Systems Offered for Sale in the Underground Economy
SCADA, Supervisory Control and Data Acquisitions, are computer systems that control various real-world equipment . These machines are crucial parts of production lines, power plants and nuclear facilities. They were relatively unknown, even to information security experts, that was until Stuxnet was detected. Stuxnet, a malware supposedly developed by […] .
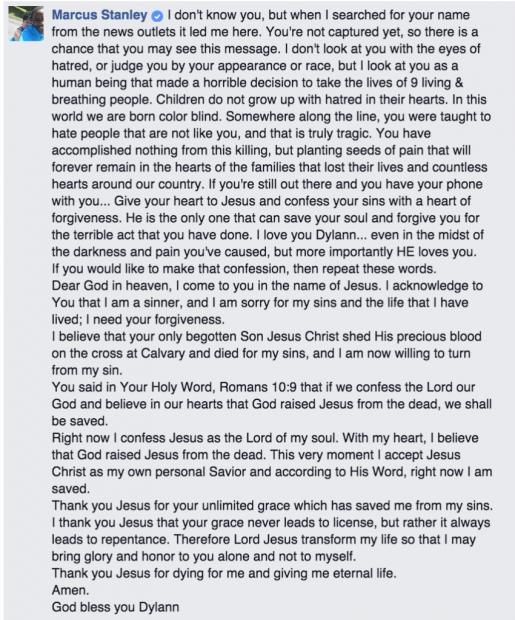
Charleston Shooting: Reactions On and Off Social Media
Whenever tragedies such as the shooting at the Emmanuel AME church in Charleston, South Carolina occur, reaction on social media is swift. Aside from the fact that users on Twitter identified the suspect long before the FBI publicly identified him , social media seems to have become the platform […] .
Edinburgh police force builds social media engagement with Lego anti-burglar scenes
Edinburgh police force builds social media engagement with Lego anti Edinburgh West Police have launched a social media campaign to inform web users how to avoid being burgled by building visual and educational scenes using Lego. The social media campaign was focused on raising awareness among Twitter users of […] .
What happens when criminal law meets neuroscience?
Robert J. Szczerba is the CEO of X Tech Ventures, an innovative company focused on solving some of today’s most challenging problems through the integration of technologies from multiple, diverse domains. This post originally appeared on Forbes. Transformative technology marks the progress of humanity. It also inevitably raises questions. […] .
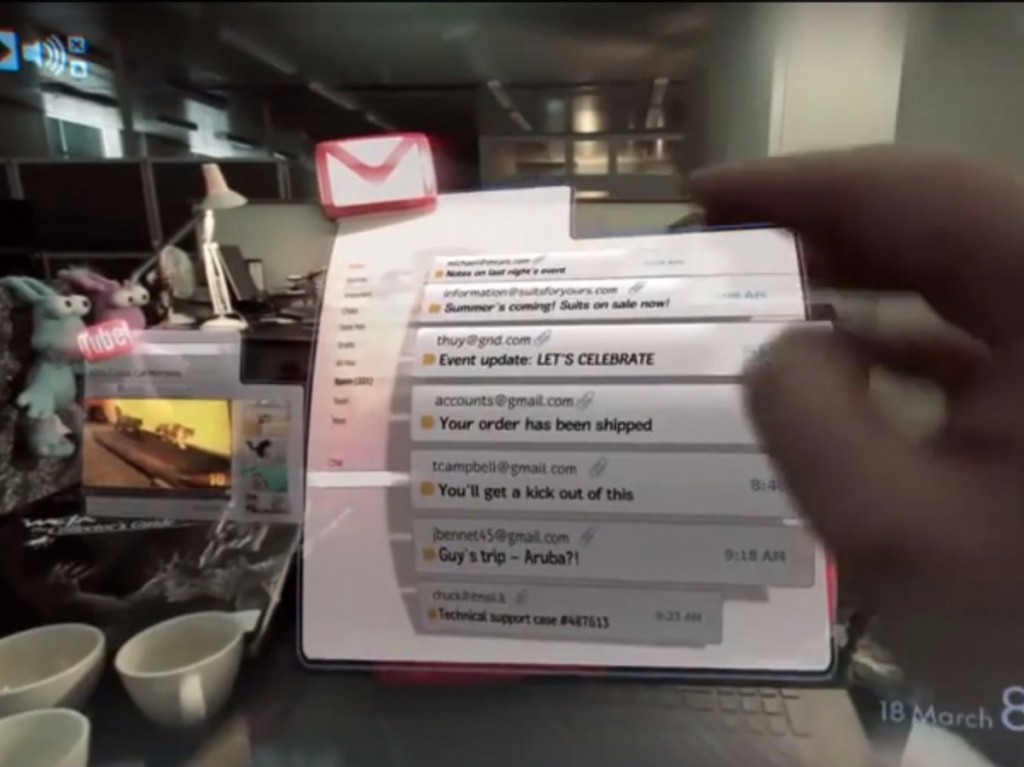
Check out this insane video of virtual reality gaming made by Google-backed Magic Leap
Magic Leap AR preview Magic Leap, the mysterious augmented reality startup with $542 million in funding by Google , just released a video that gives a glimpse into what its technology can do. Titled “Just another day in the office of Magic Leap,” the short clip shows augmented reality […] .
The staggering reach of ISIS: Report reveals it has more than 46,000 Twitter accounts
In this June 16, 2014 file photo, demonstrators chant pro-Islamic State group, slogans as they carry the group’s flags in front of the provincial government headquarters in Mosul, 225 miles (360 kilometers) northwest of Baghdad. A new report documenting the scale of the social media strategy of Islamic State […] .